Only a few days ago, we were approached by an owner of a small WooCommerce website; it seems like his WordPress website has been infected with malware. As a result, his homepage served pop-ups to the site visitors while his admin logins were compromised and changed.
After being locked out from the WordPress Dashboard, the owner searched for a WordPress malware cleanup service, and we were more than happy to take the chance and remove malware from another WordPress site.
Below we will write down the steps we took to clean up the site and some of the malware Indicators of Compromise(IoC) we found while auditing the site.
The first thing we did and always do is inspect the website files, MySQL Database and Backend of any malware injections, hidden admin users and plugins being used as backdoors.
One of the first things we noticed is that the wp-config.php has been injected with the following include:
/*1dbb5*/
@include ("/home/site/homedir/wp-content/maintenance/assets/.3f55f987.inc");
/*1dbb5*/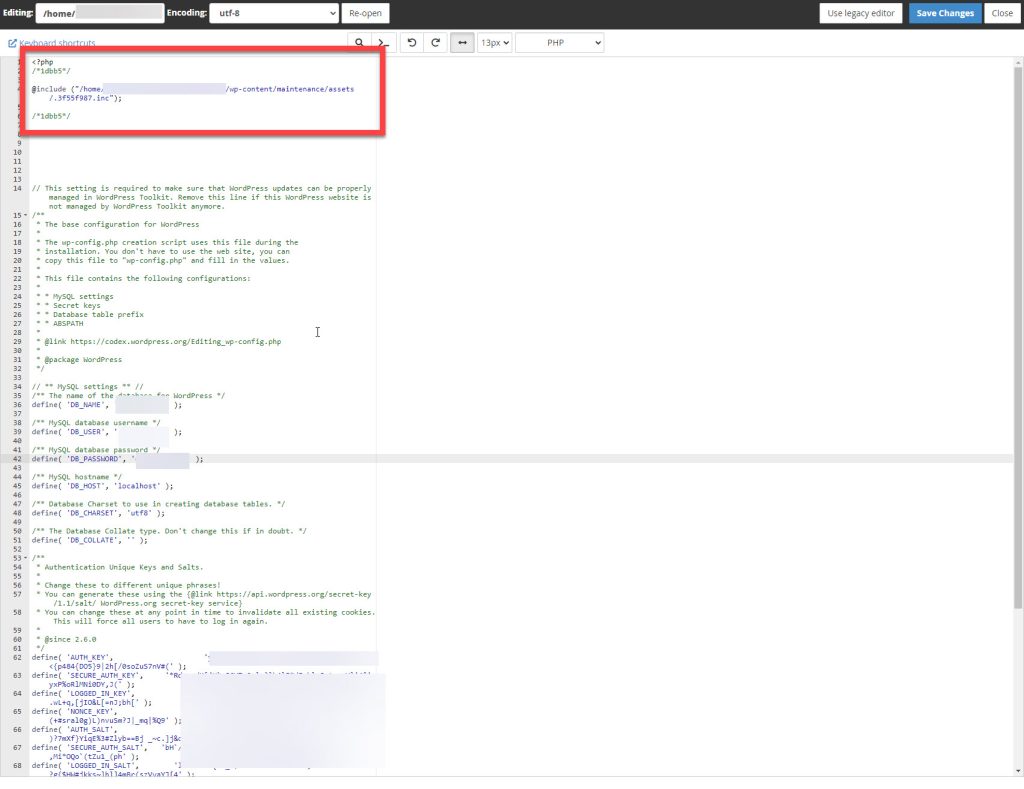
We also noticed that its public_html directory had several strangely named dirs which don’t belong to the WP default directory structure.
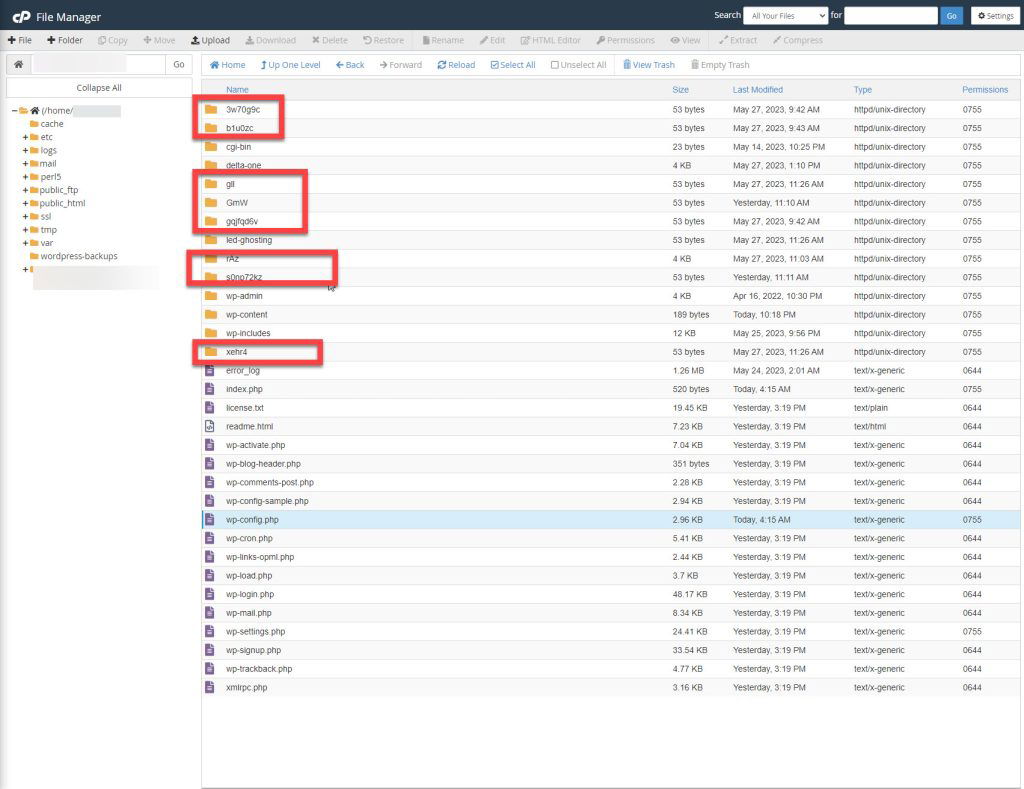
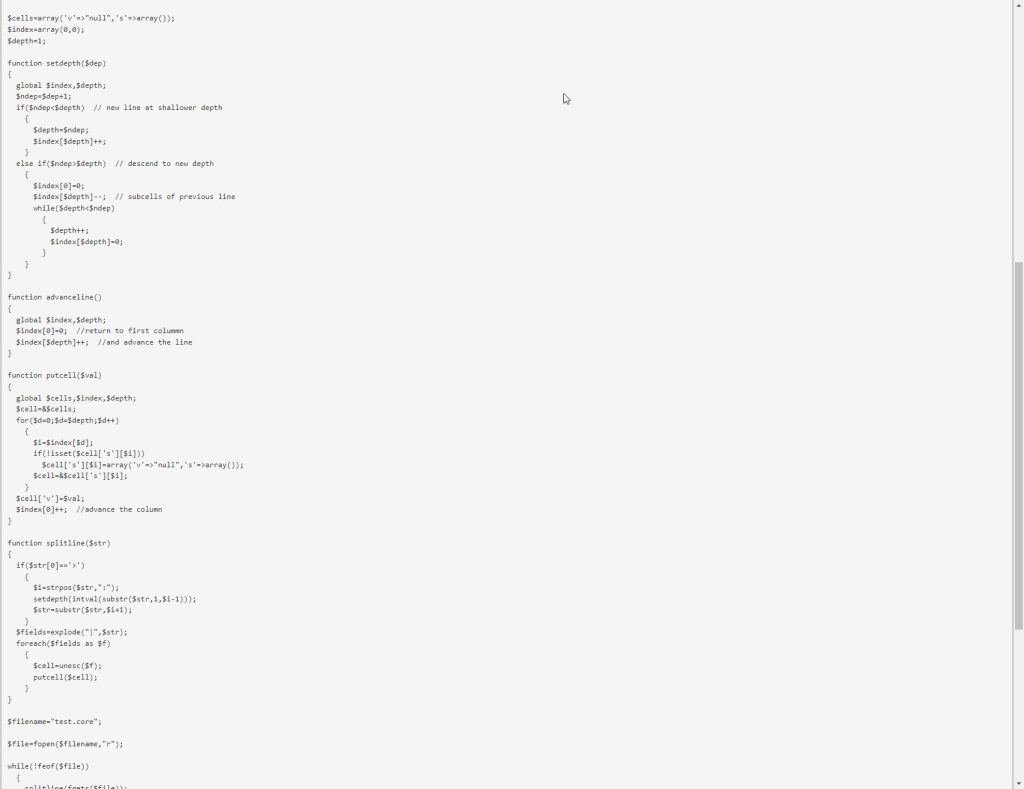
Most of those directories contained additional malware files, which we removed altogether, for example:
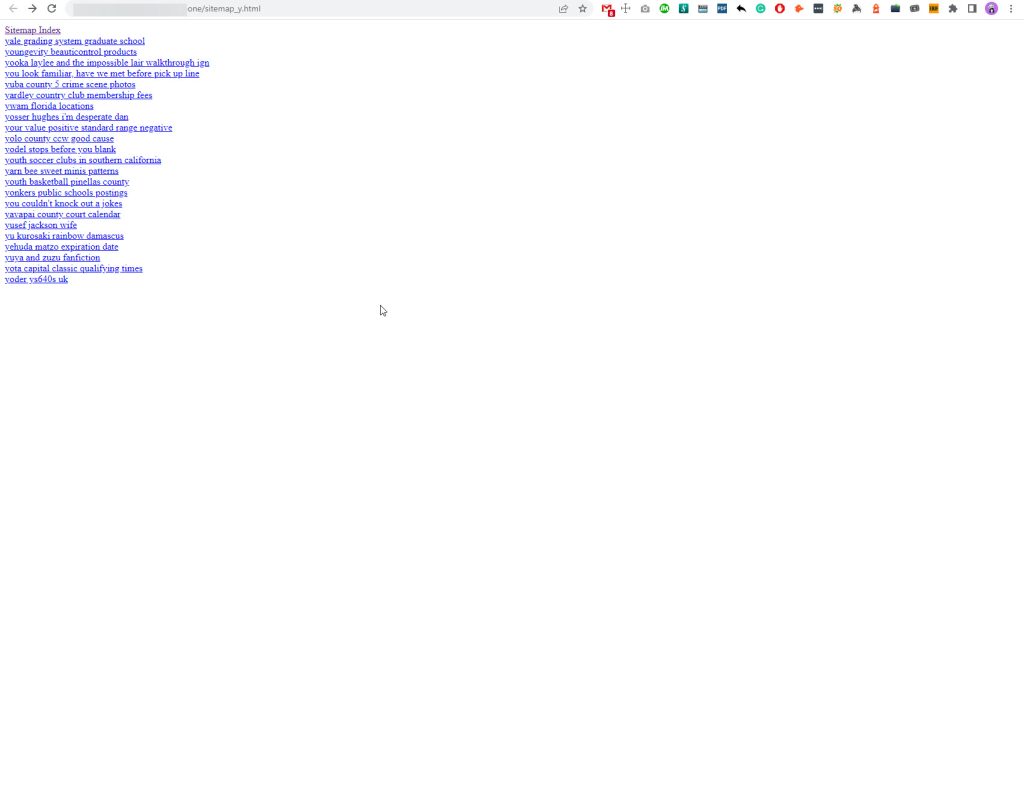
One of those rogue directories was used for promoting other websites through Black Hat SEO techniques; you can check out several of those pages along with the sitemap in the screenshots below.
Navigating through the site’s File Manager, we spotted a rogue theme entry as well, which was used as a backdoor from the hackers, newer and older ones.
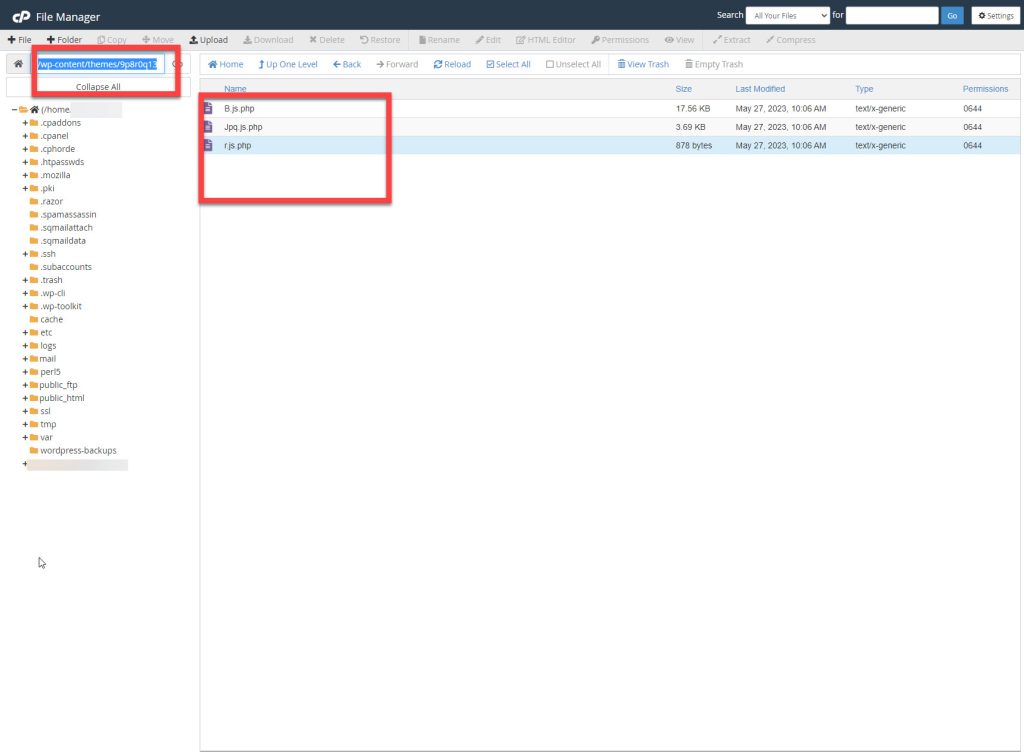
The same malicious entry has been found within the plugin directory as well.
After removing all malicious files, we ran all pending updates, removed inactive themes and plugins and re-generated the site’s Sitemap, which we later re-submitted to Google Sitemaps Service.
Another day, another infected WordPress site is malware-free!
And what was the cause of the hack? A plugin that had not been updated?
This is the case for most of the incidents we deal with.